Cybercriminals Abuse Google Cloud Email Feature in Multi-Stage Phishing Campaign
Cybersecurity researchers have disclosed details of a phishing campaign that involves the attackers impersonating legitimate Google-generated…

The ROI Problem in Attack Surface Management
Attack Surface Management (ASM) tools promise reduced risk. What they usually deliver is more information. Security…

Transparent Tribe Launches New RAT Attacks Against Indian Government and Academia
The threat actor known as Transparent Tribe has been attributed to a fresh set of attacks…

New VVS Stealer Malware Targets Discord Accounts via Obfuscated Python Code
Cybersecurity researchers have disclosed details of a new Python-based information stealer called VVS Stealer (also styled…

Bitfinex Hack Convict Ilya Lichtenstein Released Early Under U.S. First Step Act
Ilya Lichtenstein, who was sentenced to prison last year for money laundering charges in connection with…

The State of Cybersecurity in 2025: Key Segments, Insights, and Innovations
Featuring: Cybersecurity is being reshaped by forces that extend beyond individual threats or tools. As organizations…

⚡ Weekly Recap: IoT Exploits, Wallet Breaches, Rogue Extensions, AI Abuse & More
The year opened without a reset. The same pressure carried over, and in some places it…

Kimwolf Android Botnet Infects Over 2 Million Devices via Exposed ADB and Proxy Networks
The botnet known as Kimwolf has infected more than 2 million Android devices by tunneling through…

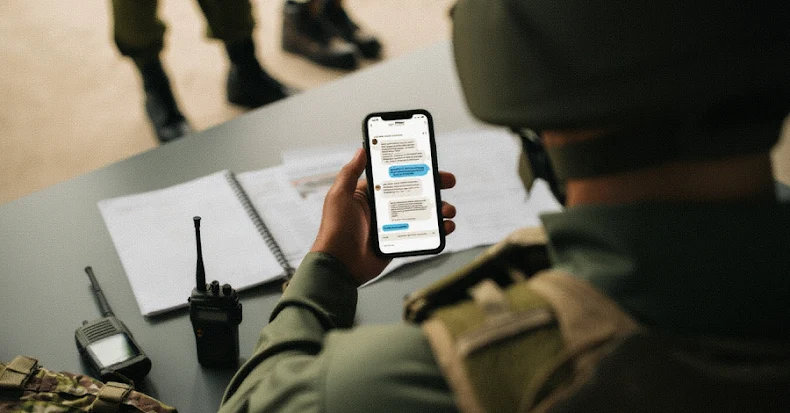
Russia-Aligned Hackers Abuse Viber to Target Ukrainian Military and Government
The Russia-aligned threat actor known as UAC-0184 has been observed targeting Ukrainian military and government entities…

Critical AdonisJS Bodyparser Flaw (CVSS 9.2) Enables Arbitrary File Write on Servers
Users of the “@adonisjs/bodyparser” npm package are being advised to update to the latest version following…
Follow Us