Malicious Chrome Extension Steals MEXC API Keys Disguised as Trading Tool
Chrome extension ‘MEXC API Automator’ steals MEXC API keys, enables withdrawals, sends credentials to attackers via…

Long-Running Web Skimming Campaign Steals Credit Cards From Online Checkout Pages
Cybersecurity researchers have discovered a major web skimming campaign that has been active since January 2022,…

CISA Flags Microsoft Office and HPE OneView Bugs as Actively Exploited
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws impacting Microsoft…

The State of Cybersecurity in 2025: Key Segments, Insights, and Innovations
Featuring: Cybersecurity is being reshaped by forces that extend beyond individual threats or tools. As organizations…

Researchers Uncover Service Providers Fueling Industrial-Scale Pig Butchering Fraud
Cybersecurity researchers have shed light on two service providers that supply online criminal networks with the…

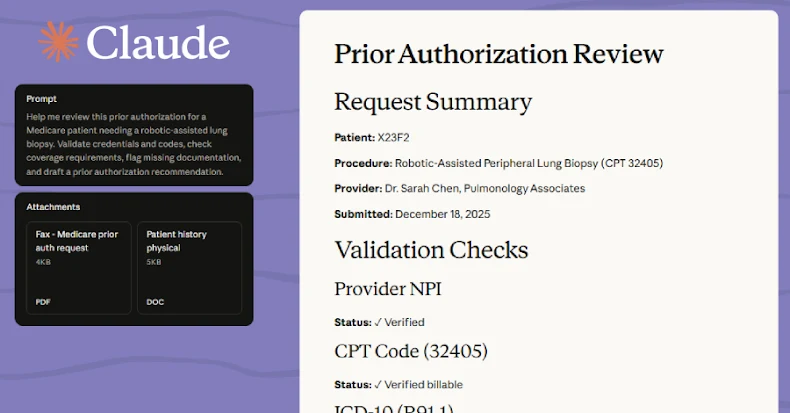
Anthropic Launches Claude AI for Healthcare with Secure Health Record Access
Anthropic has become the latest Artificial intelligence (AI) company to announce a new suite of features…

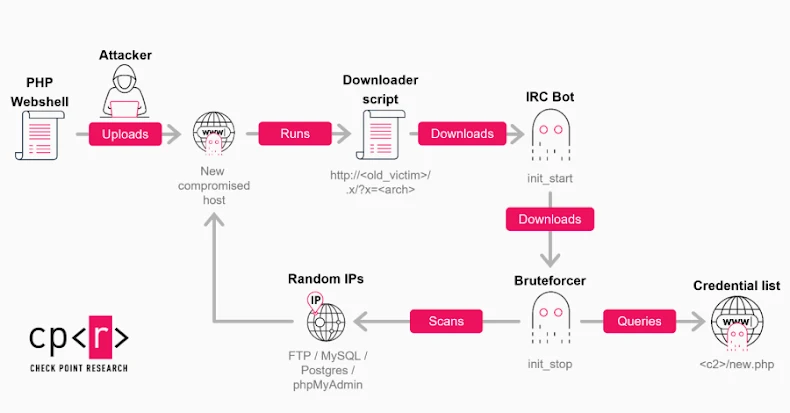
GoBruteforcer Botnet Targets Crypto Project Databases by Exploiting Weak Credentials
A new wave of GoBruteforcer attacks has targeted databases of cryptocurrency and blockchain projects to co-opt…

⚡ Weekly Recap: AI Automation Exploits, Telecom Espionage, Prompt Poaching & More
This week made one thing clear: small oversights can spiral fast. Tools meant to save time…

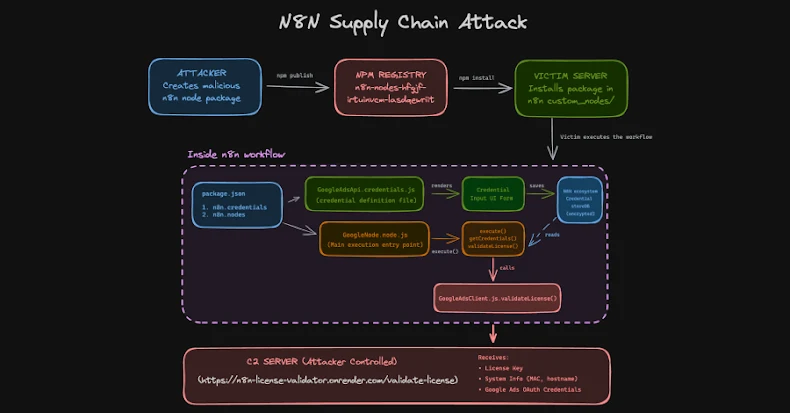
n8n Supply Chain Attack Abuses Community Nodes to Steal OAuth Tokens
Threat actors have been observed uploading a set of eight packages on the npm registry that…

MuddyWater Launches RustyWater RAT via Spear-Phishing Across Middle East Sectors
The Iranian threat actor known as MuddyWater has been attributed to a spear-phishing campaign targeting diplomatic,…
Follow Us