IsVerified Emerges with Voice Deepfake Detection Apps
IsVerified launches voice deepfake detection apps to combat AI-generated audio fraud and manipulation. The company aims…
Vulnerability Management Startup DepthFirst Raises $40 Million
DepthFirst, a vulnerability management startup, has raised $40 million in funding to help organizations prioritize and…

CISA Flags Microsoft Office and HPE OneView Bugs as Actively Exploited
CISA adds Microsoft Office and HPE OneView vulnerabilities to its KEV list, urging agencies to patch…
![[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl](data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI5MDAiIGhlaWdodD0iNDcwIiB2aWV3Qm94PSIwIDAgOTAwIDQ3MCI+PHJlY3Qgd2lkdGg9IjEwMCUiIGhlaWdodD0iMTAwJSIgc3R5bGU9ImZpbGw6I2NmZDRkYjtmaWxsLW9wYWNpdHk6IDAuMTsiLz48L3N2Zz4=)
[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl
Learn how to secure Agentic AI agents, MCPs (Machine Control Protocols), shadow API keys, and prevent…

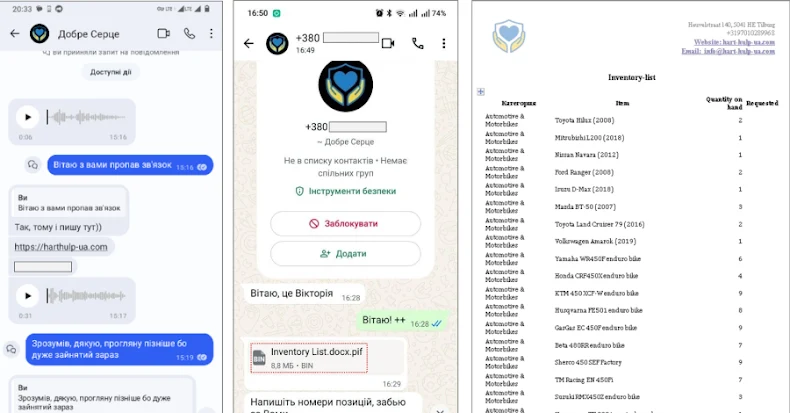
PLUGGYAPE Malware Targets Ukrainian Defense via Signal and WhatsApp
PLUGGYAPE malware targets Ukrainian defense forces via Signal and WhatsApp using phishing and evolving backdoors. Attributed…

New Research: 64% of 3rd-Party Applications Access Sensitive Data Without Justification
A study of 4,700 websites finds 64% of third-party apps access sensitive data without business need,…

AI Agents Becoming Authorization Bypass Paths: A Security Risk
AI agents in enterprises boost automation but pose authorization bypass risks due to broad permissions and…

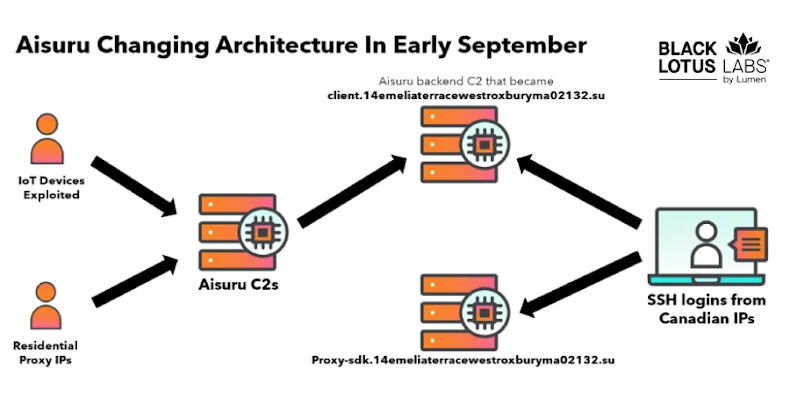
Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
Lumen Technologies null-routed traffic to over 550 C2 nodes of AISURU/Kimwolf botnet targeting millions of Android…

Microsoft Disrupts RedVDS Cybercrime Infrastructure Used for Fraud
Microsoft legal action shuts down RedVDS, a crimeware service used for phishing and BEC fraud, affecting…

4 Outdated Habits Destroying Your SOC’s MTTR in 2026
Leading SOCs reduce MTTR and MTTD by using automated, behavior-based analysis instead of manual reviews and…
Follow Us


![[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl](https://thesecreport.news/wp-content/uploads/2026/01/featured-1237-20260115-203909.jpg)