Automate Just-In-Time Access to Apps with Tines
Tines shows how automated workflows can grant, track, and revoke temporary app access without manual effort,…
New Reprompt Attack Silently Siphons Microsoft Copilot Data
A novel reprompt attack allows malicious actors to silently siphon sensitive data from Microsoft Copilot, highlighting…
IsVerified Emerges with Voice Deepfake Detection Apps
IsVerified launches voice deepfake detection apps to combat audio-based disinformation and fraud. The apps aim to…
Depth Security Raises $40 Million for Vulnerability Management
Depth Security secures $40 million in funding to advance its vulnerability management solutions and expand its…
AI Agents Tested: SQLi Success, Security Control Failures
AI agents show promise in cybersecurity, but struggle with security controls. Testing reveals strengths in SQLi,…
Stack Warp Attack Targets Confidential VMs on AMD Processors
New Stack Warp attack threatens confidential VMs on AMD processors. Learn about the vulnerability and its…
Cybersecurity Predictions and Priorities for 2026
Explore cybersecurity leaders’ predictions for 2026. Stay ahead of future threats and adapt your defenses.

CISA Flags Microsoft Office and HPE OneView Bugs as Actively Exploited
CISA adds Microsoft Office and HPE OneView vulnerabilities to its KEV list, urging agencies to patch…
![[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl](data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI5MDAiIGhlaWdodD0iNDcwIiB2aWV3Qm94PSIwIDAgOTAwIDQ3MCI+PHJlY3Qgd2lkdGg9IjEwMCUiIGhlaWdodD0iMTAwJSIgc3R5bGU9ImZpbGw6I2NmZDRkYjtmaWxsLW9wYWNpdHk6IDAuMTsiLz48L3N2Zz4=)
[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl
AI agents now build and run software automatically. Insecure MCPs and CVE-2025-6514 show how trusted automation…

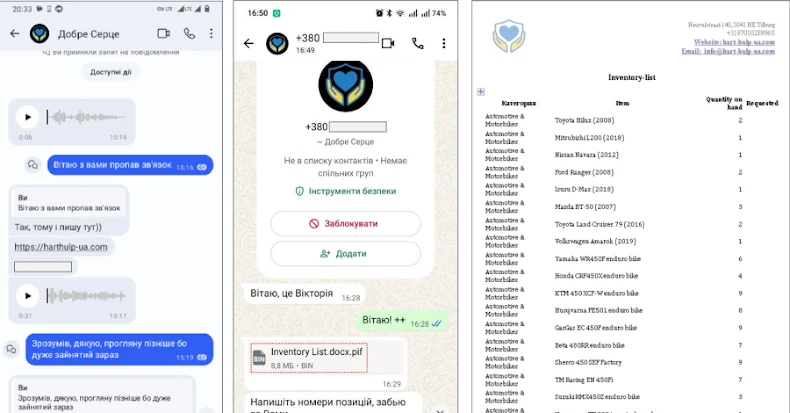
PLUGGYAPE Malware Targets Ukrainian Defense Forces via Signal, WhatsApp
PLUGGYAPE malware attacks Ukrainian defense forces using Signal, WhatsApp phishing links and evolving backdoors. CERT-UA reports.…
Follow Us



![[Webinar] Securing Agentic AI: From MCPs and Tool Access to Shadow API Key Sprawl](https://thesecreport.news/wp-content/uploads/2026/01/featured-1264-20260115-203839.jpg)