AI Agents Are Becoming Authorization Bypass Paths
Enterprise AI agents boost automation but often run with broad permissions, allowing actions beyond user access…

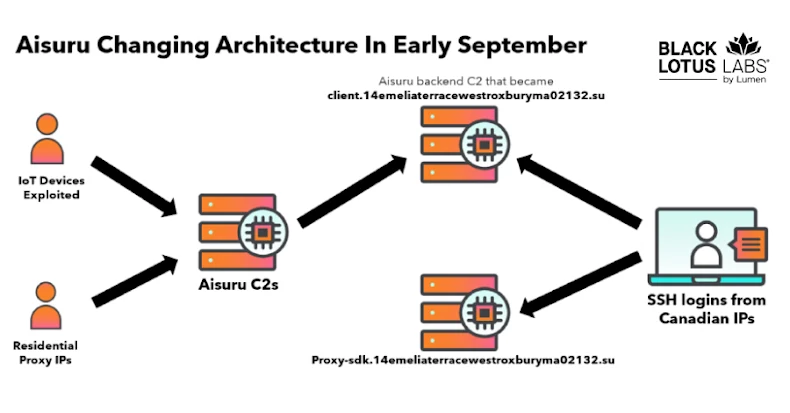
Researchers Null-Route Over 550 Kimwolf and Aisuru Botnet Command Servers
Lumen Technologies null-routed traffic to over 550 Kimwolf/AISURU C2 nodes, disrupting the massive DDoS botnet of…

Microsoft Disrupts RedVDS Cybercrime Infrastructure Preventing Online Fraud
Microsoft’s legal action disrupts RedVDS, a crimeware service used for fraud, preventing millions in losses and…

Researchers Expose Reprompt Attack Enabling Data Theft from Microsoft Copilot
Reprompt attack allows data exfiltration from Microsoft Copilot via URL parameter manipulation. Microsoft has addressed the…

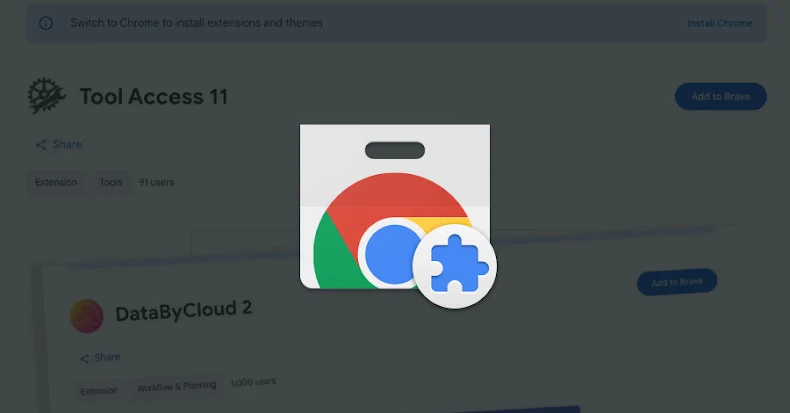
Malicious Chrome Extensions Impersonate Workday and NetSuite
Fake Chrome extensions impersonate Workday, NetSuite. Steal cookies, block admin controls, hijack sessions for account takeover.

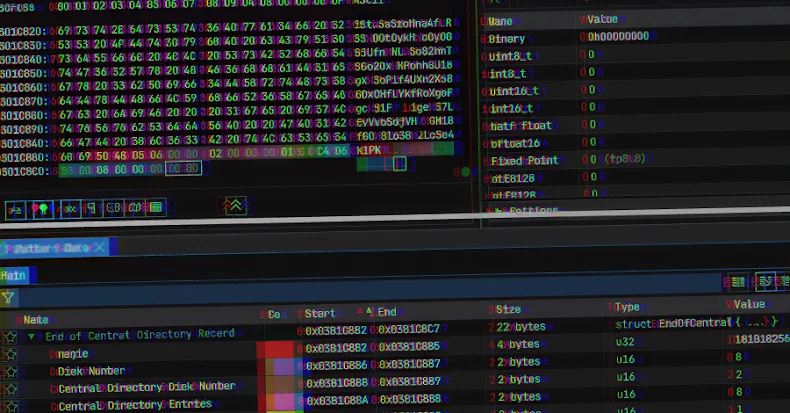
GootLoader Malware Uses ZIP Archive Concatenation to Evade Detection
GootLoader malware uses malformed ZIP archives with 500-1,000 concatenations to evade detection, delivering JavaScript payloads via…

Drones to Diplomas: Russia’s University Linked to $25M Essay Mill
Krebs reveals how Russia’s largest private university, linked to the Kremlin, ties into a $25M essay…

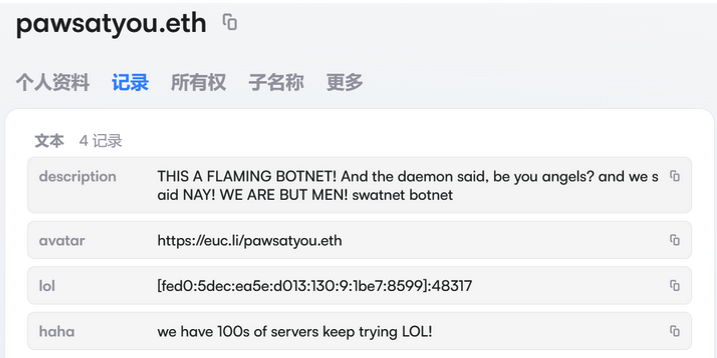
Who Benefited from the Aisuru and Kimwolf Botnets?
A deep dive into the Kimwolf botnet and the actors who profited from its spread, including…

Verizon Wireless Outage Blamed on Software Issue Affecting Nationwide Service
Verizon confirms nationwide wireless outage was due to a software issue. The company apologizes and offers…

Gootloader Uses 1,000-Part ZIP Archives for Stealth Delivery
Gootloader malware now uses a malformed ZIP archive with up to 1,000 concatenated archives to evade…
Follow Us