Cybersecurity researchers have shed light on two service providers that supply online criminal networks with the necessary tools and infrastructure to fuel the pig butchering-as-a-service (PBaaS) economy.
At least since 2016, Chinese-speaking criminal groups have erected industrial-scale scam centers across Southeast Asia, creating special economic zones that are devoted to fraudulent investment and impersonation operations.
These compounds are host to thousands of people who are lured with the promise of high-paying jobs, only to have their passports and be forced to conduct scams under the threat of violence. INTERPOL has characterized these networks as human trafficking-fuelled fraud on an industrial scale.
One of the crucial drivers of the pig butchering (aka romance baiting) scams is service providers who supply the networks with all the tools to run and manage social engineering operations, as well as swiftly launder stolen funds and cryptocurrencies and move ill-gotten proceeds to accounts that cannot be reached by law enforcement.
“Large scam compounds such as the Golden Triangle Economic Zone (GTSEZ) are now using ready-made applications and templates from PBaaS providers,” Infoblox said in a report published last week.
“Compounding the situation further, what once required technical expertise, or an outlay for physical infrastructure, can now be purchased as an off-the-shelf service offering everything from stolen identities and front companies to turnkey scam platforms and mobile apps, dramatically lowering the barrier to entry.”
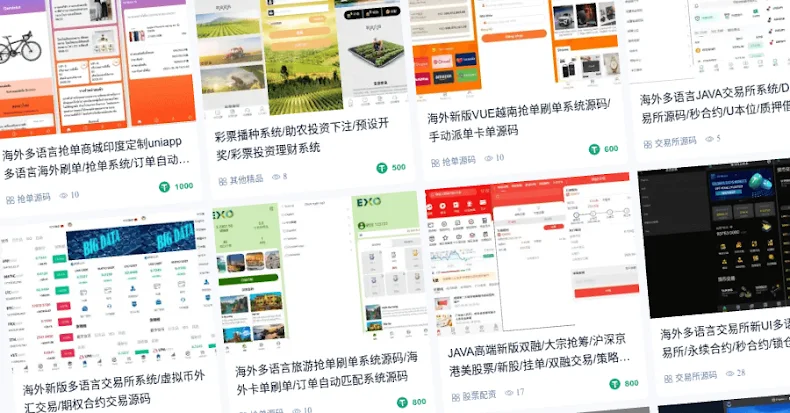
These services have been found to offer full packages and fraud kits that set the groundwork for launching scalable online scam operations without much effort. One such threat actor is Penguin Account Store, which also goes by the names Heavenly Alliance and Overseas Alliance.
Penguin operates under a crimeware-as-a-service (CaaS) model, advertising fraud kits, scam templates, and “shè gōng kù” datasets comprising stolen personal information belonging to Chinese citizens. The group also peddles account data from various popular so-called media platforms like Twitter, Tinder, YouTube, Snapchat, Facebook, Instagram, Apple Music, OpenAI ChatGPT, Spotify, and Netflix, among others.
It’s believed that these credentials are likely obtained through information-stealing logs sold on the dark web. But it’s presently not known if they operate the stealers themselves or whether they are merely acting as a broker of stolen data for other threat actors. Prices for pre-registered social media accounts start from just $0.10 and go up in value depending on the date of registration and authenticity.
Also provided by Penguin are bulk pre-registered SIM cards, stolen social media accounts, 4G or 5G routers, IMSI catchers, and packages of stolen pictures (aka character sets) that are used to entrap victims. Besides these, the threat actor has developed a Social Customer Relationship Management (SCRM) platform dubbed SCRM AI to allow scam operators to facilitate automated victim engagement on social media.
“The threat actor also advertises BCD Pay, a payment processing platform. BCD Pay, which links directly to the Bochuang Guarantee (博创担保自), is an anonymous peer-to-peer (P2P) solution à la HuiOne, with deep roots in the illegal online gambling space.”
A second service category that’s central to the PBaaS economy is customer relationship management (CRM) platforms, which provide centralized control over several individual agents. UWORK, a seller of content and agent management tools, provides pre-made templates for creating investment scam websites. Many a scam offering also claims to have integration with legitimate trading platforms like MetaTrader to lend the sites a veneer of trust by displaying real-time financial information.
These websites also come fitted with a Know Your Customer (KYC) panel that requires victims to upload proof of their identity. The websites’ settings are configured by an administrator through a dedicated panel, granting them a high-level view of the entire operation, along with the ability to create profiles for agents, who likely interface with the victims.