Attack Surface Management (ASM) tools promise reduced risk. What they usually deliver is more information.
Security teams deploy ASM, asset inventories grow, alerts start flowing, and dashboards fill up. There is visible activity and measurable output. But when leadership asks a simple question, “Is this reducing incidents?” the answer is often unclear.
This gap between effort and outcome is the core ROI problem in attack surface management, especially when ROI is measured primarily through asset counts instead of risk reduction.
The Promise vs. The Proof
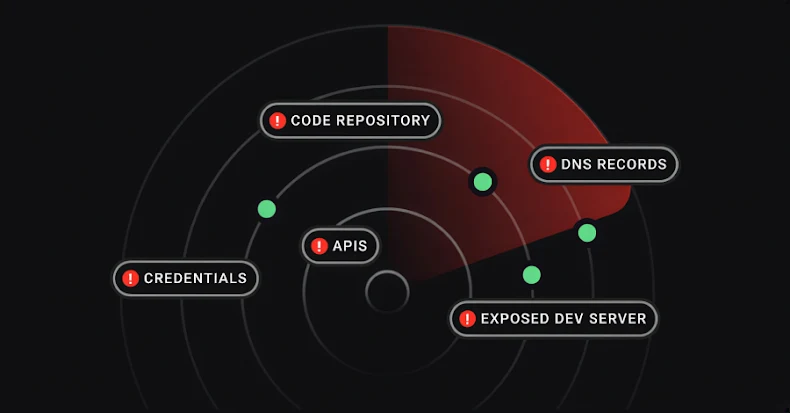
Most ASM programs are built around a reasonable idea: you can’t protect what you don’t know exists. As a result, teams focus on discovery: domains and subdomains, IPs and cloud resources, third-party infrastructure, and transient or short-lived assets.
Over time, counts increase. Dashboards are trending upward. Coverage improves.
But none of those metrics directly answer whether the organization is actually safer. In many cases, teams end up busier without feeling less exposed.
Why ASM Feels Busy but Not Effective
ASM tends to optimize for coverage because coverage is easy to measure: more assets discovered, more changes detected, and more alerts generated. Each of those feels like progress.
But they mostly measure inputs, not outcomes.
In practice, teams experience:
- Alert fatigue
- Long backlogs of “known but unresolved” assets
- Repeated ownership confusion
- Exposure that lingers for months
The work is real. The risk reduction is harder to see.
The Measurement Gap
One reason ASM ROI is hard to prove is that most attack surface metrics focus on what the system can see, not what the organization actually improves.
Common attack surface management metrics include:
- Number of assets
- Number of changes
More meaningful attack surface metrics are rarely tracked:
- How fast risky assets get owned
- How long dangerous exposure persists
- Whether attack paths actually shrink over time
Asset inventory remains foundational to measuring the external attack surface. Without broad discovery, it’s impossible to understand exposure at all. The gap appears when discovery metrics aren’t paired with measurements that show whether risk is actually being reduced.
Without outcome-oriented measurements, ASM becomes difficult to defend during budget reviews, even when everyone agrees that asset visibility is necessary.
What Would Meaningful ROI Look Like?
Instead of asking, “How many assets did we discover?” a more useful question is, “How much faster and safer did we get at handling exposure?”
That reframing shifts ROI from visibility to response quality and exposure duration. Things that correlate much more closely with real-world risk.
Three Outcome Metrics That Actually Matter
1. Mean Time to Asset Ownership
How long does it take to answer the basic question: “Who owns this?”
Assets without clear ownership:
- Linger longer
- Get patched later
- Are more likely to be forgotten entirely
Reducing time-to-ownership shortens the window where exposure exists without accountability. It’s one of the clearest signals that ASM findings are turning into action.
2. Reduction in Unauthenticated, State-Changing Endpoints
Not all assets matter equally.
Tracking how many external endpoints can change state, how many require authentication, and how those numbers change over time provides a much stronger signal of whether the attack surface is shrinking where it counts.
An environment with thousands of static assets but few unauthenticated, state-changing paths is meaningfully safer than one with fewer assets but many risky entry points.
3. Time to Decommission After Ownership Loss
Exposure often persists after:
- Team changes
- Application deprecation
- Vendor migrations
- Reorgs
Measuring how quickly assets are retired once ownership disappears is one of the strongest indicators of long-term hygiene and one of the least commonly tracked.
If abandoned assets stick around indefinitely, discovery alone isn’t reducing risk.
What This Looks Like in Practice
Abstract metrics are easy to agree with and hard to operationalize. The goal isn’t a new dashboard or a different set of alerts, but a shift in what’s made visible: ownership gaps, exposure duration, and unresolved risk that would otherwise blend into asset counts.