The Black Lotus Labs team at Lumen Technologies said it null-routed traffic to more than 550 command-and-control (C2) nodes associated with the AISURU/Kimwolf botnet since early October 2025.
AISURU and its Android counterpart, Kimwolf, have emerged as some of the biggest botnets in recent times, capable of directing enslaved devices to participate in distributed denial-of-service (DDoS) attacks and relay malicious traffic for residential proxy services.
Details about Kimwolf emerged last month when QiAnXin XLab published an exhaustive analysis of the malware, which turns compromised devices – mostly unsanctioned Android TV streaming devices – into a residential proxy by delivering a software development kit (SDK) called ByteConnect either directly or through sketchy apps that come pre-installed on them.
The net result is that the botnet has expanded to infect more than 2 million Android devices with an exposed Android Debug Bridge (ADB) service by tunneling through residential proxy networks, thereby allowing the threat actors to compromise a wide swath of TV boxes.
A subsequent report from Synthient has revealed Kimwolf actors attempting to offload proxy bandwidth in exchange for upfront cash.
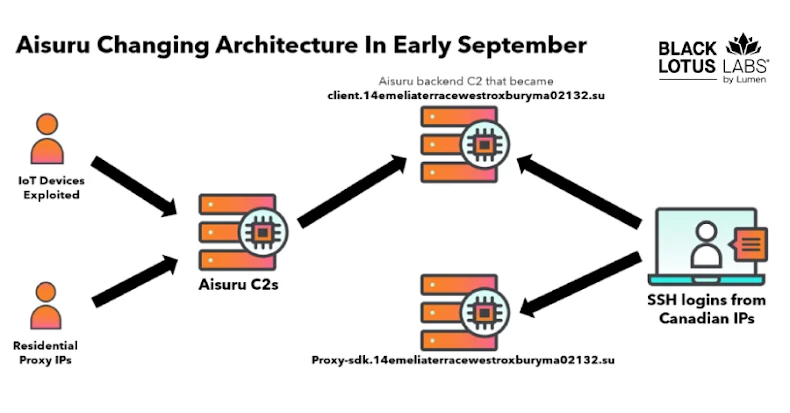
Black Lotus Labs said it identified in September 2025 a group of residential SSH connections originating from multiple Canadian IP addresses based on its analysis of backend C2 for Aisuru at 65.108.5[.]46, with the IP addresses using SSH to access 194.46.59[.]169, which proxy-sdk.14emeliaterracewestroxburyma02132[.]su.
It’s worth noting that the second-level domain surpassed Google in Cloudflare’s list of top 100 domains in November 2025, prompting the web infrastructure company to scrub it from the list.
Then, in early October 2025, the cybersecurity company said it identified another C2 domain – greatfirewallisacensorshiptool.14emeliaterracewestroxburyma02132[.]su – that resolved to 104.171.170[.]21, an IP address belonging to Utah-based hosting provider Resi Rack LLC. The company advertises itself as a “Premium Game Server Hosting Provider.”
This link is crucial, as a recent report from independent security journalist Brian Krebs revealed how people behind various proxy services based on the botnets were peddling their warez on a Discord server called resi[.]to. This also included Resi Rack’s co-founders, who are said to have been actively engaged in selling proxy services via Discord for nearly two years.
The server, which has since disappeared, was owned by someone named “d” (assessed to be short for the handle “Dort”), with Snow believed to be the botmaster.
“In early October, we observed a 300% surge in the number of new bots added to Kimwolf over a 7-day period, which was the start of an increase that reached 800,000 total bots by mid-month,” Black Lotus Labs said. “Nearly all of the bots in this surge were found listed for sale on a single residential proxy service.”
Subsequently, the Kimwolf C2 architecture was found to scan PYPROXY and other services for vulnerable devices between October 20, 2025, and November 6, 2025 — a behavior explained by the botnet’s exploitation of a security flaw in many proxy services that made it possible to interact with devices on the internal networks of residential proxy endpoints and drop the malware.
This, in turn, is suspected of facilitating a surge in botnet sizes by effectively dropping a Kimwolf client on vulnerable devices.
The Lumen analysis also discovered Kimwolf infrastructure interacting with other botnet-related services, including those associated with AISURU, AndroidGate, and Mirai.
In light of the abuse, Black Lotus Labs said it has taken steps to disrupt the botnets by null-routing traffic to more than 550 C2 nodes used by Kimwolf and Aisuru, effectively severing the connection between infected devices and their controllers. This action aims to prevent the botnets from being used for DDoS attacks or malicious traffic relay.
“We appreciate Lumen’s action against the Kimwolf and AISURU botnets,” Krebs said. “These botnets are a menace to the Internet at large, and all the more insidious given that many of the people renting access to these botnets likely have little understanding of how they’re assembled — let alone who benefits from their misuse.”
“Dort being involved also makes the matter all the more interesting given that he and Snow were previously known to be the administrators behind the Moobot botnet,” Krebs added.
The findings come as the Microsoft Threat Intelligence Center (MSTIC) disclosed details of an unclassified report that sheds light on Pyongyang-backed hacking groups engaging in a vast range of malicious activities, including intelligence collection, theft of cryptocurrency assets, and supply chain attacks.